The web is currently dominated by more software than ever, and your application is only one of the vast number of software deployed on the web. If you want to find ways of efficiently securing your dev and operations pipelines to make your app’s user experience stand out, this article is exactly what you need. In this article, I will introduce you to how you can secure your pipelines in Azure DevOps, which will improve the security of your application.
Table of Contents
Azure DevOps
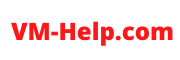
Azure DevOps provides services tailored to the support teams to enable them to plan work effectively, collaborate on code development, and build and deploy applications or softwares. To complement the development of the software, Azure DevOps offers a collection of processes that brings developers, project/product managers, and contributors together.
With Azure DevOps, organizations can develop and improve applications at a quicker pace than when using traditional software development approaches. It provides many features that you can access through your web browser or integrated development environment (IDE). You can use one or more of Azure Repos, Azure Pipelines, Azure Boards, Azure Test Plans, or Azure Artifacts. We will be focusing on the Azure Pipelines feature in Azure DevOps.
Azure Pipelines
Azure Pipelines builds and tests software projects automatically to make them accessible to others. It works with just about any programming language or project type. Azure Pipelines merges continuous integration (CI) with continuous delivery (CD) and continuous testing (CT) to test and build your code and deploy it to the cloud. A pipeline simply defines the CI/CD process for your app. It contains one or more stages. You can think of it as a workflow that establishes how your test, build, and deployment steps are run.
Securing Your Azure Pipelines
The following tips can help you deal with security risks in your Azure DevOps pipeline and ensure that any open source vulnerabilities are handled effectively.
1. Scan your Containers
Scanning your containers in Azure DevOps pipelines can help you pinpoint vulnerable configurations, infectious malware, insufficient secrets management, and breach of compliance. This step should be performed periodically during the development process.
Ensure that all containers are scanned. All containers include the ones in which your pipeline services and software are developed, tested, or deployed. Another good idea is to scan any master images you may be building the environment from. An effective approach is to fix vulnerabilities at the source rather than address issues each time a container is deployed to the cloud.
2. Runtime Protection Implementation
The reason you should implement runtime protections is to protect your software against the vulnerabilities you are yet to identify and those you are unable to secure, like the operating systems of your host containers. To be absolutely sure of this protection, you should use strong access control and verify that users have the minimum requisite privileges.
Ensure that you are also addressing the protection of runtime in your applications. You can use Runtime Application Self-Protection (RASP) to secure applications during runtime with an automated tool.
RASP continuously inspects traffic to the application and dynamically blocks any traffic that indicates malicious or suspicious activity as it functions as a security framework inside the application. When you use RASP, you are protecting your application against SQL injections, vulnerabilities, cross-site scripting (XSS), bots, and other web applications attacks.
A security framework like RASP should be attached at the beginning of the software development life cycle (SDLC) so that your application will be secure by default. To enhance your project’s security, deploy applications and DevOps pipelines with the RASP tool included.
3. Access Management Privileges
Limit access rights privilege to decrease potential attacks. For example, you can limit developers’ and testers’ access to specific areas. On end-user devices, you can remove administrator privileges and establish a workflow check-out process. These steps help reduce the risk of persons getting unauthorized access to sensitive information and control of the system.
4. Supply Chain Security of Software
Developers more often than not use open-source frameworks, libraries, and codes to improve speed and efficiency. There are millions of open source projects that give convenient access to ready-to-use functionalities. However, integrating open source modules into the software supply chain can create many challenges for security teams.
Security teams need to prevent open source vulnerabilities in DevOps supply chains with concise guidelines and policies. You should encourage all software dependencies visibility by using build automation tools. Container technology can also help segregate vulnerabilities and decrease possible damage.
Make sure you do automated vulnerability scans on dependencies while developing and testing applications. This looks for security issues. Most software nowadays use external libraries or packages from open source components that can have libraries or packages with known vulnerabilities. Most of the time, developers forget to check these things.
To help with this, you should consider some free tools that can automate tasks and streamline processes.
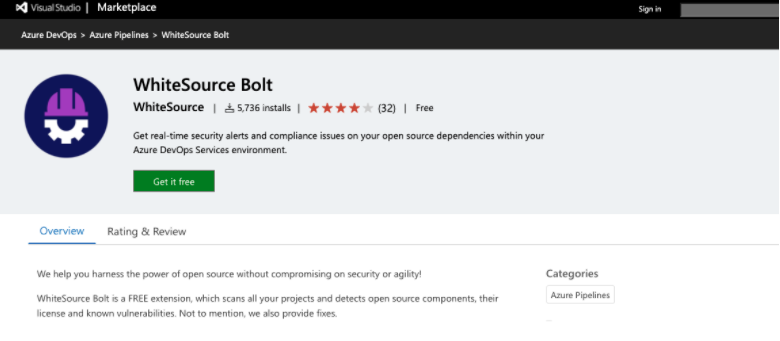
For example, WhiteSource Bolt works by providing security alerts, flagging compliance issues, and finding and fixing open source vulnerabilities in your Azure DevOps pipeline.
It seamlessly integrates with your existing workflows in Azure DevOps to obtain comprehensive data on security vulnerabilities in your application and suggests solutions to address them—its vulnerability database is best in class. In addition, it obtains licensing data on used modules in Azure DevOps. You can find this tool in the Azure DevOps marketplace.
5. Monitoring the Pipeline
To ensure the protection of your pipelines and various environments, a centralized monitoring tool is critical. Centralization tools, like system information and event management (SIEM) solutions, can facilitate aggregate log data and alerts for you.
These tools aggregate log data and alerts and correlate event data to you, which in turn provides transparency into the way the pipeline functions and how secure it is. When there is no centralization, issues and incidents are more likely to be missed.
Final Thoughts
In summation, better security measures in pipelines are a huge part of the development and operations process and shouldn’t be ignored. Your team should always prioritize security.